KM in project-based & temporary organisations: Part 7 – The risk library approach and how it relates to the risk causation model
This article is part 7 in a series of articles on knowledge management (KM) in project-based and temporary organisations.
In the previous part (part 6) of this series, I summarized research1 by Zhu and colleagues proposing a “risk causation model” to capture and transfer project knowledge. This model has obvious parallels with lessons learned processes, but is much more comprehensive.
I recommend further research and development in regard to the risk causation model, given that I have previously successfully used a similar “risk library” approach in a major environmental program. This program was the $77.4 million Hawkesbury-Nepean River Recovery Program (HNRRP), which had the aim of improving the health of an iconic river system in New South Wales (NSW), Australia. The program comprised seven projects carried out by six different NSW Government agencies.
I commenced in the role of overall Program Manager of the HNRRP in June 2009. The program concluded two and a half years later, having exceeded its intended outcomes. It was completed on time and under budget, despite significant challenges, and subsequently won two major awards. One of the keys to this success was the risk management approach that I decided should be implemented.
I had long been concerned about the risk management approaches that I had seen used in environmental projects in Australia, which had typically involved the project team or leaders convening a brief meeting where the group was asked the question “What do you think are the risks faced by this project, and what should we do about them?” This approach limits the exploration of potential risk to the knowledge of those present in the room. While the knowledge of the group may be substantial, it still has its limits. Not only will there be aspects of risk that are beyond the experiences and awareness of the group, but such a basic process won’t even trigger participants to reveal all that they do know. This makes such an approach to risk management a risk in itself.
With this in mind, and acutely aware that the HNRRP was highly politically sensitive with ambitious outcomes to be achieved within a short time frame and fixed maximum budget, I sought to identify and implement the best possible approach to risk management.
 As summarized on page 9 of part 1 of the HNRRP final report, my research led me to the “risk library” approach used by Gerry Robinson, author of the book Risk Thinkers Guide: The Breakthrough Book on Risk Management2 and previously the risk manager for the Sydney 2000 Olympics. The risk library approach also accorded with the then Australian Risk Management Standard AS/NZS 4360:2004 (which has since been superseded). Gerry Robinson was subsequently engaged to facilitate the risk assessment for the HNRRP.
As summarized on page 9 of part 1 of the HNRRP final report, my research led me to the “risk library” approach used by Gerry Robinson, author of the book Risk Thinkers Guide: The Breakthrough Book on Risk Management2 and previously the risk manager for the Sydney 2000 Olympics. The risk library approach also accorded with the then Australian Risk Management Standard AS/NZS 4360:2004 (which has since been superseded). Gerry Robinson was subsequently engaged to facilitate the risk assessment for the HNRRP.
Rather than being limited by the knowledge of a group, the risk library approach ensures that the widest range of possible risks are thoroughly explored. The elements of the risk library align closely with the “situational variables” and “risk path” of Zhu and colleagues’ risk causation model, as discussed in part 6.
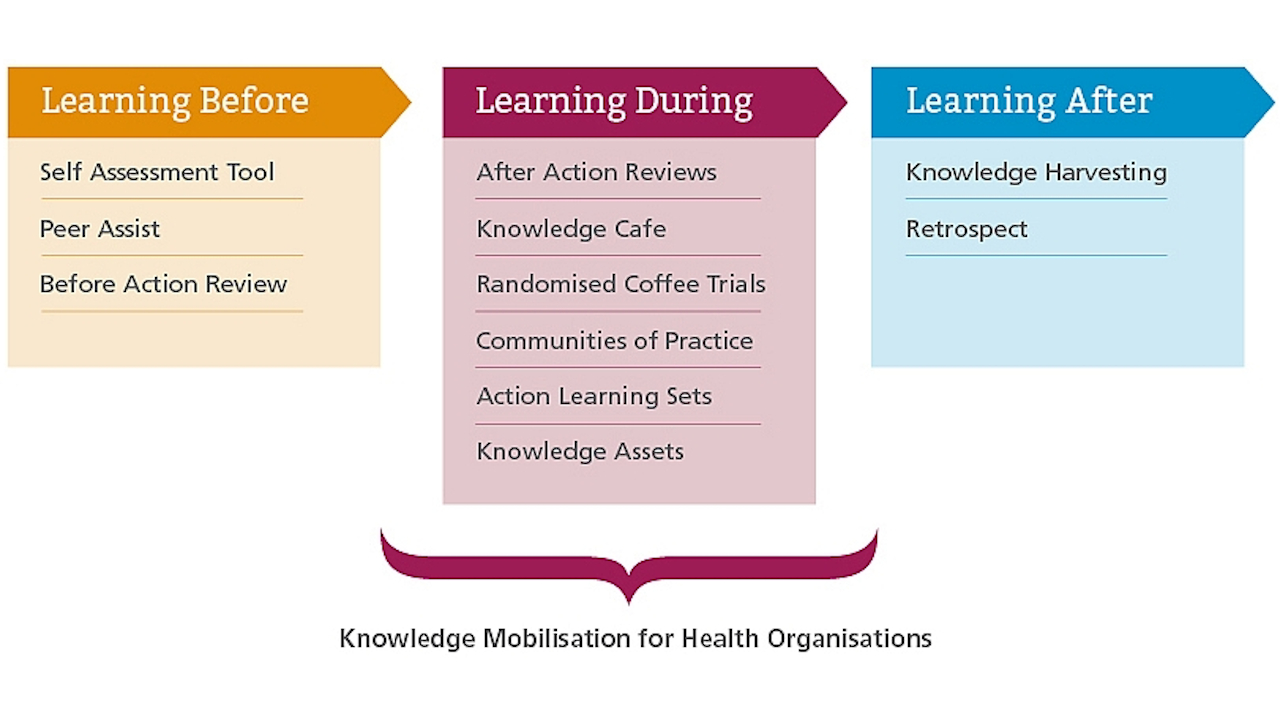
Risk library risk assessment process
The first step in the HNNRP risk assessment was a three-hour workshop to develop the risk assessment framework and commence the assessment process.
The workshop participants included:
- project managers and key staff from all seven projects of the HNRRP
- representatives from the Australian Government department that was funding the HNRRP
- NSW Government Office of the Hawkesbury-Nepean, which was the overall program management body (and where I worked).
The workshop agenda included:
- conducting stakeholder and SWOT analyses
- developing a risk ranking matrix
- reviewing the project risk library to agree which risks are generic to all projects and which require individual assessment and documentation.
The risk library consisted of 63 known potential risks under the categories of:
- commercial
- business process
- financial
- human resources
- information
- property
- environmental
- health and safety
- insurable risk.
As part of the SWOT analysis, the following new business overview risks were identified and responsibility for their management allocated to me as the Program Manager:
- community engagement
- communication framework
- project inter-dependency
- funding deed compliance
- scope and cost.
The second step of the HNNRP risk assessment involved the project managers of the seven component projects of the HNRRP separately convening similar risk library workshops with their teams. The outcomes of these workshops were reported back to a further workshop involving all of the participants from the first workshop.
The final outcome of the risk assessment was a report listing all relevant risks for both the overall HNRRP and its component projects, the ranking of each risk, and controls and actions for each risk.
Risk library risk review process
As discussed in part 6, Zhu and colleagues’ risk causation model couples a risk management process with a risk repository through a risk review structure. They define risk review as “the formal review when risks occur that captures key risk experiences for improving risk management for the current and future projects.”
In the HNRRP, the capturing of key risk experiences for improving risk management for the current program and its seven component projects was achieved through the three-monthly agile program management cycle of the HNRRP. This agile program management approach is discussed in part 8, which is recommended reading alongside this article.
However, the capturing of key risk experiences for improving risk management for future programs and projects was only done in an unstructured way, for example by communicating some of these experiences through the final report. Ideally, the comprehensive risk library that had been developed and evolved through the program and its component projects could have formed the basis for the ongoing and regularly updated risk repository proposed by Zhu and colleagues.
Header image source: Alvaro Reyes on Unsplash.
Reference:
- Zhu, F., Hu, H., & Xu, F. (2022). Risk causation model to capture and transfer knowledge in international construction projects. Journal of Civil Engineering and Management, 28(6), 457-468. ↩
- Robinson, G, (2006). Risk Thinkers Guide: The Breakthrough Book on Risk Management. Melbourne: Brolga Publishing. ↩
Also published on Medium.